What is Microsoft Defender for Office 365? (A Beginner’s Guide)
December 12th, 2023 | 4 min. read
Editor's note: This post was originally published on December 14, 2021 and has been revised for clarity and comprehensiveness.
Choosing the best Microsoft products can feel like blindly grabbing socks from your closet and hoping they match. With all the options available, how do you decide which product is the best for your company?
When it comes to security, you don’t want to have a product that underperforms your business or doesn’t help with the problem you have.
Intelligent Technical Solutions (ITS) has been in the business for over 20 years, and we fully understand that choosing the best security program is vital for small companies. So, we’ve prepared an article about Microsoft Defender for Office 365.
We’ll tackle the following points:
- The definition of Microsoft Defender for Office 365
- The features and plans of Microsoft Defender for Office 365
- A quick comparison of Microsoft Defender for Office 365 with other Microsoft Defender products
By the end of this article, you’ll have an easier time choosing which Microsoft Defender product you can use for your business.
What is Microsoft Defender for Office 365?
Microsoft Defender for Office 365 (formerly known as Office 365 Advanced Threat Protection) is a security service designed to protect you when you use Office 365.
According to Microsoft, it’s a cloud-based email filtering service that protects your business from threats to email & collaboration tools.
Essentially, Defender for Office 365 targets threats that can be coursed through your use of Office 365. It’s connected to a database from Microsoft that analyzes your correspondence and evaluates the likelihood of a link or file being a virus.
Microsoft Defender for Office 365 Features
This program primarily focuses on threat prevention, investigation, and response in the Office 365 workspace. Defender for Office 365 comes with different plan levels that are often bundled with the kind of Microsoft subscription you have.
However, it’s possible to upgrade to a different Defender for Office 365 plan separately. This is great for businesses that have specialized needs.
There are two possible plans for Defender for Office 365: Plan 1 and Plan 2.
Defender for Office: Plan 1
Plan 1 for Defender for Office is a step up from the standard EOP (Exchange Online Protection). EOP focuses on basic threat detection and prevention, while Plan 1 builds on EOP features by expanding on threat prevention and detection.
The main features of Plan 1 are:
 1. Safe Attachments
1. Safe Attachments
Defender can quickly scan the attachments in communication among your organization's users.
 2. Safe Links
2. Safe Links
Defender can use Microsoft’s database to test links in a controlled environment and see any suspicious activities.
 3. Safe Attachments for SharePoint, OneDrive, and Microsoft Teams
3. Safe Attachments for SharePoint, OneDrive, and Microsoft Teams
Plan 1 protects SharePoint, OneDrive, and Microsoft Teams attachments, unlike EOP, which has more limitations.
 4. Anti-phishing in Defender for Office 365 protection
4. Anti-phishing in Defender for Office 365 protection
There is an additional layer of protection against phishing. Defender points out or quarantines communication that suspiciously asks you to provide information.
 5. Real-time detection
5. Real-time detection
The ability to see threats in real-time allows for SIEM (Security Information and Events Management) Integration.
Defender for Office: Plan 2
Plan 2 of Defender for Office 365 contains all the features of Plan 1 & EOP. It expands on the previous plans by focusing on security education, threat investigation, threat response, and automation of security protocols.
The main additional features of Plan 2 are:
 1. Threat Trackers
1. Threat Trackers
Threat tracking allows you to see the path of a threat across your organization. It can provide invaluable insight into possible security breaches in your system.
 2. Threat Explorer
2. Threat Explorer
Threat Explorer provides a deeper analysis of threats in real-time against people in your organization.
 3. Automated investigation and response
3. Automated investigation and response
Automated threat detection helps free up your IT personnel's time to deal with threats that need human judgment.
 4. Attack simulation training
4. Attack simulation training
To highlight the thrust for a holistic security program, Defender for Office Plan 2 includes training. Attack simulation training helps staff have a proactive role in managing their security.
Defender for Office 365 vs. Endpoint vs. Identity vs. Cloud Apps
The problem with Defender for Office 365 is distinguishing it from the other Microsoft Defender products, which can seem confusing at first glance.
Think of Defender products like a hierarchy.
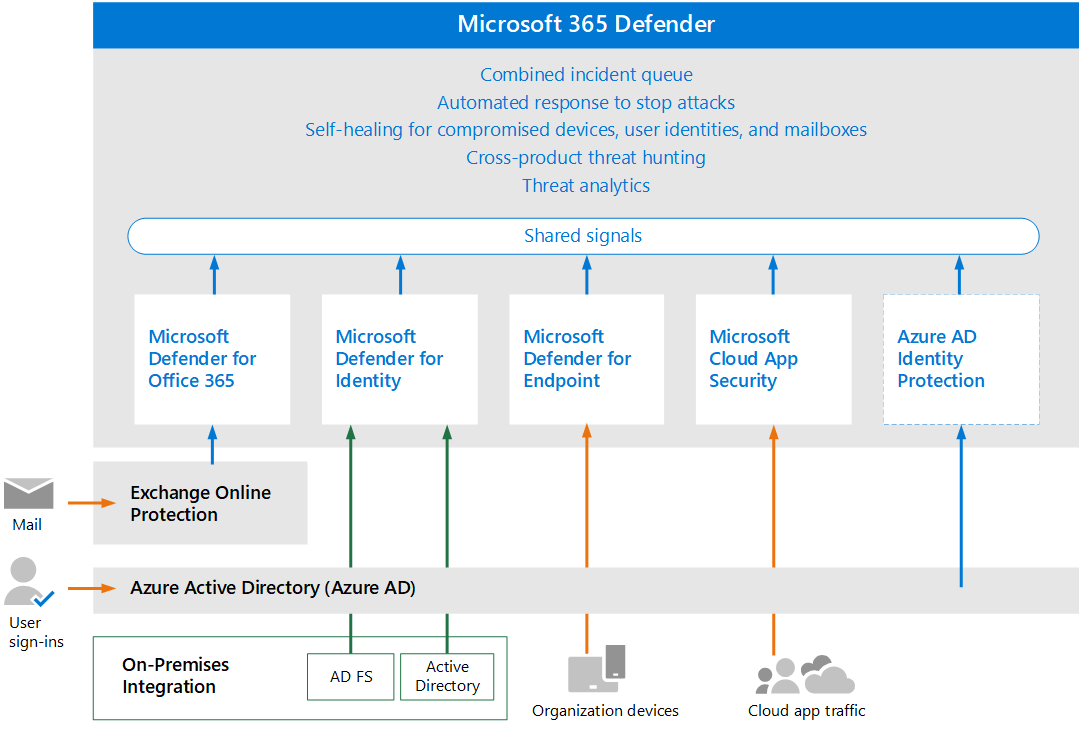
At the top is Microsoft Defender. This is the integrated dashboard that has the following services:
- Defender for Office 365
- Defender for Endpoint
- Defender for Identity
- Defender for Cloud Apps
These products were formerly called other names but have been standardized in recent months by Microsoft.
Microsoft 365 Defender architecture
Each Defender product has its own specialization:
1. Defender for Office
Defender for Office focuses on threats that come through your use of Office 365. This is best for companies that rely on Office 365.
2. Defender for Identity
Defender for Identity (formerly Defender for Azure) leverages user behavior and active directory analysis to see possible identity-based security threats.
3. Defender for Endpoint
Defender for Endpoint specializes in endpoint threats. It uses AI (Artificial Intelligence) to evaluate threats to your system.
4. Defender for Cloud Apps
Defender for Cloud Apps (formerly known as Cloud App Security) focuses on analyzing the security of the deployed cloud apps in your organization.
Ready to implement Microsoft Defender for your business?
All in all, Microsoft Defender is a powerful tool to protect your company’s data. Defender for Office 365 protects your users when they use Office 365 programs.
It’s best to have this if your organization relies heavily on Office 365 for your employees.
However, if your business isn’t reliant on it, or is too small to benefit from a plan, you can use the standard protection offered by Microsoft.
Making the correct choice of where to put your company resources is no easy task. And ITS, as a Microsoft Gold partner, specializes in helping clients get the best Microsoft products that fit their company. We’ve prepared the following resources to help you find the best Microsoft tools for your company:
- What’s the Right Microsoft Office 365 Plan for My Business?
- Pros and Cons of Using Microsoft 365 Suite for Your Business
- Should I Get Microsoft 365 with an MSP? (7 Key Benefits)
- eBook: 3 Types of Cyber Security Solutions Your Business Must Have
But we also know that having an idea of what Microsoft products are available isn’t enough to get a holistic security setup for your IT infrastructure. Learn more about your company’s security needs with our free IT needs analyzer. You can also schedule a call with one of our cybersecurity consultants.
Kharmela Mindanao is a senior content writer for Intelligent Technical Solutions. She’s called Ella by her friends and likes yoga, literature, and mountain climbing. Her favorite book is Anxious People by Fredrik Backman. She creates art and poetry and is on a quest to find the best cheesecake.
Topics: