How to Implement MFA for Email Exchange Servers
August 2nd, 2022 | 3 min. read
%20(30).jpg)
Keeping emails private might sound like a simple task, but that's far from the truth in today's threat landscape. That's because cybercriminals have a lot to gain from attacking your email accounts. It's the reason scams like spoofing, phishing, and social engineering are all geared toward gaining access to them. Your company's email data is valuable; protecting it should be a top priority.
Thankfully, multi-factor authentication (MFA) is one of the most affordable but impactful ways to protect yourself from identity-related cyber attacks. It virtually eliminates unauthorized access from brute force attacks and other methods that leverage stolen passwords. A massive improvement considering it's estimated that 81% of data breaches are due to poor password security.
If that sounds too good to be true, here's the caveat: It only works when it's configured properly. A tricky challenge when you're implementing it on something like an email exchange server.
At ITS, we are a security-focused managed service provider (MSP) dedicated to helping businesses learn how to protect their data. In this article, we'll take a look at the different methods and steps you can take to implement MFA.
Implement MFA for Exchange Online
Implementing MFA for all cloud-based apps through Microsoft's Azure Active Directory (AD) is pretty straightforward. You can do it manually through the Azure portal, or you can enforce it for all by enabling Security Defaults. That will force everyone on your network to use MFA and block legacy authentication, drastically improving your security. However, it's not perfect.
Security Defaults will make a lot of configuration changes to your network, and some of those might cause issues across your system. For example, if you are still using legacy applications that can't support modern authentication methods, you may experience problems using them after enabling Security Defaults.
Microsoft has already rolled out Security Defaults for everyone. That means if your systems are up-to-date, you should already have yours enabled or configured. However, if your systems are older, you should expect a notification from Microsoft informing you that Security Defaults will automatically enable unless you explicitly reject it.
Implement MFA for On-Premises Exchange Servers
Here's where implementing MFA can get tricky. Your old exchange on-premises servers are no longer compatible with Integrated Windows Authentication (IWA) and Azure AD. That means if you want to implement MFA, you'll have to be creative. You can do that by integrating Azure AD with Microsoft's Single Sign-On solution called Active Directory Federation Services (ADFS).
ADFS was originally designed to authenticate users into applications that were outside the Windows ecosystem and the organization's perimeter. It allowed identity information to be shared securely outside of your company's network so you could access web-facing resources that were hosted by organizations you trusted. However, it also allows you to register users for Azure MFA with ADFS.
To do that, however, you first need to meet the following requirements:
- Windows Server 2016 AD FS on-premises environment
- Azure subscription with Azure Active Directory.
- Azure MFA Adapter
Steps to Implement MFA for On-Premises Servers:
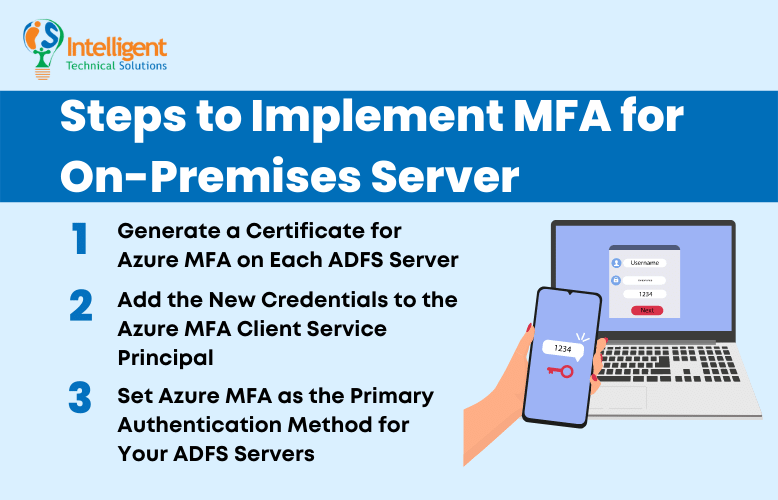
1. Generate a Certificate for Azure MFA on Each ADFS Server
The first step is to generate a certificate for Azure MFA to use. You can do that by opening a PowerShell prompt then using the following cmdlet to generate the new certificate: $certbase64 = New-AdfsAzureMfaTenantCertificate -TenantID <tenantID>
Note that TenantID is the name of your directory in Azure AD. The certificate generated can be found in the local machines certificate store, and it is marked with a subject name with the TenantID for your Azure AD directory.
2. Add the New Credentials to the Azure MFA Client Service Principal
To add the new credentials, open up PowerShell and set the certificate as the new credential against the Azure MFA Client by typing in:
New-MsolServicePrincipalCredential -AppPrincipalId 981f26a1-7f43-403b-a875-f8b09b8cd720 -Type asymmetric -Usage verify -Value $certBase64
Once the new credentials are added to the Service Principal of the Azure MFA Client, the ADFS servers will be able to communicate with it.
3. Set Azure MFA as the Primary Authentication Method for Your ADFS Servers
After completing the steps above on each ADFS server, set Azure MFA as their primary authentication method. You can do that by executing the following cmdlet on Powershell:
Set-AdfsAzureMfaTenant -TenantId <tenant ID> -ClientId 981f26a1-7f43-403b-a875-f8b09b8cd720
After that, you will see that Azure MFA will be available as a primary authentication method for intranet and extranet use.
It might seem simple, but there are a lot of factors that can make the process very tricky. For example, some Windows Servers don't have the latest service pack, which means the previous steps could fail to configure your Azure tenant. In those cases, you might have to manually create the registry entries.
If that seems too much, don't fret. Reliable IT support companies can get you through every step so you can secure your email exchange servers. There's nothing wrong with getting help from experts.
Ready to Set Up MFA for Your Email Exchange Servers?
Implementing MFA on your exchange servers is one of the most impactful and affordable ways to protect your emails. Bear in mind, however, that it only works when configured properly. It can be a straightforward process, just as when you're implementing it for cloud apps, or tricky like when you're implementing it for on-prem servers.
Hopefully, with the guide above, you'll be able to implement MFA without any problems. But don't hesitate to seek help from IT support companies if things don't go too well. A reliable MSP has the expertise and experience to get the job done right the first time.
At ITS, we've helped hundreds of businesses implement MFA across their networks and servers. Check out our article on the different types of MFA and the best MFA for your business to find the right solution for your company.
Mark Sheldon Villanueva has over a decade of experience creating engaging content for companies based in Asia, Australia and North America. He has produced all manner of creative content for small local businesses and large multinational corporations that span a wide variety of industries. Mark also used to work as a content team leader for an award-winning digital marketing agency based in Singapore.
Topics:

