Addressing Cybersecurity Risks of Working from Home
June 23rd, 2022 | 5 min. read

Working from home brings convenience to both employees and employers. It helps employees achieve better work-life balance as time and effort spent on their commute could otherwise be spent on something more productive. Your business can also enjoy reduced operational costs since fewer employees work on-premises. Those are all great benefits. However, this setup also carries a lot of risks.
Home network setups have weaker cybersecurity measures compared to a regular office. This gaping hole can be exploited by hackers to attack your business. Moreover, employees working at home don’t receive the same IT support they get when working on-premises.
Add them together, and you have a recipe for disaster right on your lap.
Here at Intelligent Technical Solutions (ITS), we help businesses prevent these problems from happening. We help create a safe and secure network for employees and employers by deploying multi-layered cybersecurity programs.
In this article, we’ll discuss the cybersecurity risks and problems of having remote workers. We’ll also share the programs you need to implement to cut those risks and how ITS helps its remote clients. After a complete read-through, you will better understand the challenges your remote workers face and ways to solve them.
Cybersecurity Risks and Problems When Working Remotely
Many businesses have implemented work-from-home setups ever since the pandemic hit. 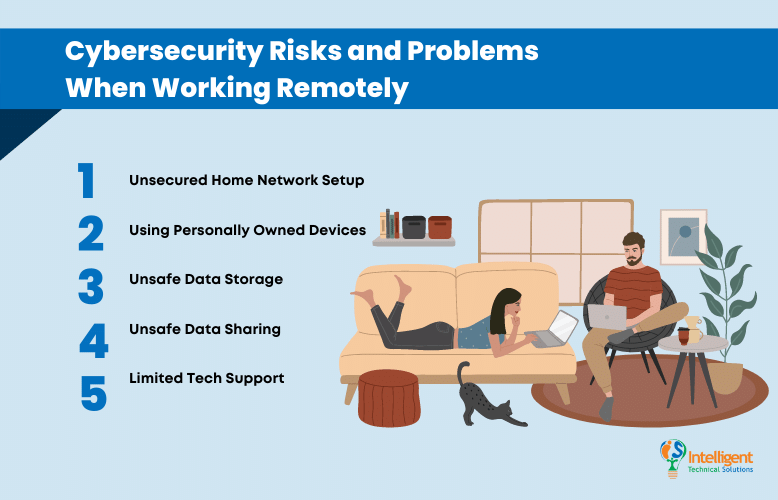 Though it brought benefits to employees, it also introduced risks that endanger your business.
Though it brought benefits to employees, it also introduced risks that endanger your business.
The following are some of them:
Unsecured Home Network Setup
The standard home network setup is not on par with what a traditional office has. First and foremost, they are not professionally managed by IT experts, so misses on security updates are commonplace.
It’s also harder to enforce security strategies and password management policies on an individual network than a traditional office Wi-Fi. That means if an individual doesn’t practice good cyber hygiene their password can easily be cracked. All that’s needed is a password cracking tool, and hackers can infiltrate your network in a few minutes. Once inside, they can install malware to steal valuable information and sell them on the dark web or use it for ransomware.
Using Personally Owned Devices
Let’s be honest, most personal devices we own are unsecured. Using them to connect to your corporate device or business network is a huge mistake as it can serve as a gateway for hackers to transfer viruses and malware. You may have not realized it yet, but the unsecured apps on your device pose a great threat to your security, and much more to your business.
Unsafe Data Storage
Thanks to encryption, files stored and shared within a corporate network are relatively safe. However, it’s a different story when working remotely. Most data storage tools at home aren’t equipped with encryption capabilities, meaning hackers can easily decipher and steal them without you realizing it.
Unsafe Data Sharing
The file-sharing services you may be using aren’t as secure as you thought. Same with storage, transferring files within a corporate network undergo encryption to prevent being hacked. But the situation is not the same when using publicly available file-sharing tools.
Unsecured file sharing allows hackers to intercept your data. If you don’t know it yet, your files are in their most vulnerable state when in transit. Like bandits in a heist film, hackers are on the lookout for essential files being moved. Once they see the right opportunity, they will strike hard.
Limited Tech Support
The problems your remote workers face don’t end with cybersecurity. In fact, one of the biggest problems remote workers face is having limited tech support. Simple issues can take hours and even days to fix as they don’t have an on-premises IT tech that they can tap for a quick assist.
According to the 2021 Velocity Smart Technology Market Research Report, 70% of remote workers experienced IT problems during the pandemic, and 54% of them waited for at least three hours to resolve them. That’s three hours of unproductivity! Can you imagine your losses if it happens to an entire team?
Tech issues shouldn’t be shrugged off. It can significantly affect your revenue and overall performance. And if left unsolved, it can stem into even more severe problems.
Addressing the Risks of Working Remotely
Fortunately, the problems we mentioned can be solved with minor tweaks to your security measures. The following are some of the services we offer in securing the network of remote workers.
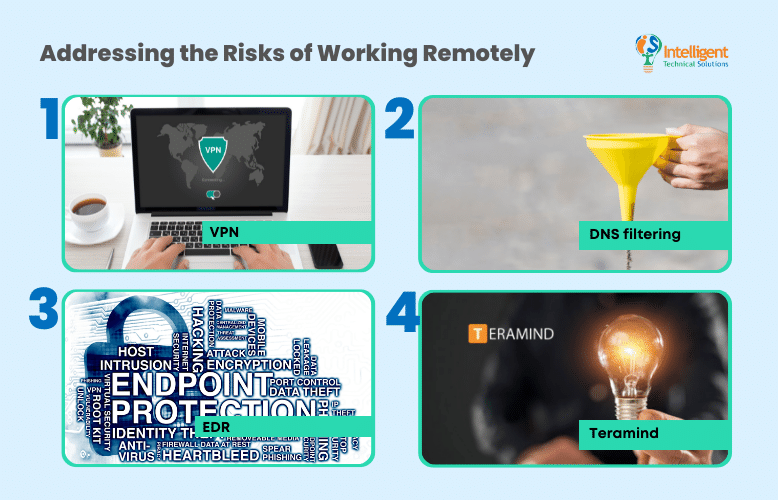
VPN
Virtual Private Network (VPN) is a service that encrypts the connection from one network to another. It is conducive for companies with remote workers as it protects your data from being intercepted by unwanted parties.
Companies deploy their setup in implementing VPNs. But in ITS, we build our infrastructure to accomplish a robust point-to-site connection. We also host our VPN server to mediate VPN connections.
To make our service even more secure, we implement multi-factor authentication (MFA) from a Microsoft Office 365 account before a user can log in.
DNS filtering
While Domain Name System (DNS) acts as the internet's phonebook, DNS filtering serves as the safety net of your network. It prevents employees from visiting malicious websites and unverified links used in phishing attacks. It means a lesser chance of malware attacks and viruses penetrating your network.
ITS offers services and tools to help your team identify DNS leaks in your network. We can also set up DNS filtering in your network to ensure its security 24-7.
EDR
Endpoint Detection and Response (EDR) is an endpoint security solution that monitors end-user devices. Its purpose is to find potential security breaches as they happen and facilitate a quick response to suppress them. It records the activities on endpoints and provides security teams with the visibility they need to expose incidents that would otherwise remain invisible.
Teramind
Teramind offers a combination of user activity monitoring and data loss functionality. It allows you to optimize workforce productivity through session recording capabilities. It can also mitigate insider threats through policy enforcement, risk analysis, reporting user actions, and Optical Character Recognition (OCR) forensics.
Have Your IT Service Provider’s Hotline Ready
 One of the significant differences between remote and traditional work setups is the support they get. Employees in an office can get instant tech support since they are on the same premise as their IT team.
One of the significant differences between remote and traditional work setups is the support they get. Employees in an office can get instant tech support since they are on the same premise as their IT team.
However, it’s a different story for remote workers. Unless you have an IT tech living with you, say your sibling or flatmate, you know how hard it is to get help when experiencing a tech issue. Employees usually resort to fixing the issues by themselves, which is harmful and may lead to other problems.
In this case, having a hotline for your IT team or IT service provider will play a crucial role in the swift resolution of your tech dilemmas. The hotline should be available to all your employees and easy to remember.
If your IT service provider doesn’t have a hotline, you may want to reconsider renewing your contract. You may also want to check the quality of their support team while at it.
Use Remote Access
We understand that remote workers experience challenges when getting tech assistance, so giving them support equivalent to on-premise IT is necessary. So how can you do it? Through Remote Access, of course!
Remote access gives technicians the capability to navigate your device remotely. This allows them to personally assess and truly understand what’s going on with your device. They can also apply the necessary fix right away so you can go back to doing what’s essential. What’s great about this method is it eliminates the back-and-forth probing that eats up much of your time.
In addition, Remote Access removes the need to bring your item on site for software updates and inspection.
Is Your Team Aware of the Cybersecurity Risks of Working from Home
Sure, there are risks with the work-from-home setup, but what format doesn’t? What’s important is you work your best to minimize them. Protect your employees and your business from threats by deploying VPN, EDS, and DNS filtering programs. You can also utilize Teramind to monitor your employee’s actions and optimize workforce productivity.
Having a hotline for your IT service provider will also help your team in dealing with their tech issues. Since they don’t have access to on-premise support, having alternatives like over-the-phone support and remote access are valuable assets.
At ITS, we help businesses ensure a secure and seamless connection with their remote workers by deploying multi-layered cybersecurity programs on their network. Our team is committed to sharing our IT knowledge with all so that you can make smart tech decisions for your business.
Learn more about how you can further streamline your remote work setup by downloading and reading our eBook entitled Top Tips to Make Remote Work effective for your Business. This eBook can serve as your guideline to making a successful remote working team!
Topics:
