7 Cybersecurity Best Practices for Remote Work
October 12th, 2022 | 4 min. read
%20(54).jpg)
Shifting trends brought by the sudden onslaught of COVID-19 made remote work a feasible choice for businesses. Not only does remote work protect employee health, but it also makes for happier employees, reduces rental costs, and promotes trust.
But remote work magnifies IT challenges you won’t often see in onsite work, and that includes cybersecurity issues.
So, how do you keep your company safe while keeping (or shifting) to a remote work set-up?
As a Managed Security Service Provider (MSSP), Intelligent Technical Solutions (ITS) knows the struggle to keep a company safe from criminals in the current tech environment. Even prior to the pandemic, we have been helping clients with remote work set-up with their cybersecurity. In fact, many of our team members also work from home, and we take care of our own remote work cybersecurity.
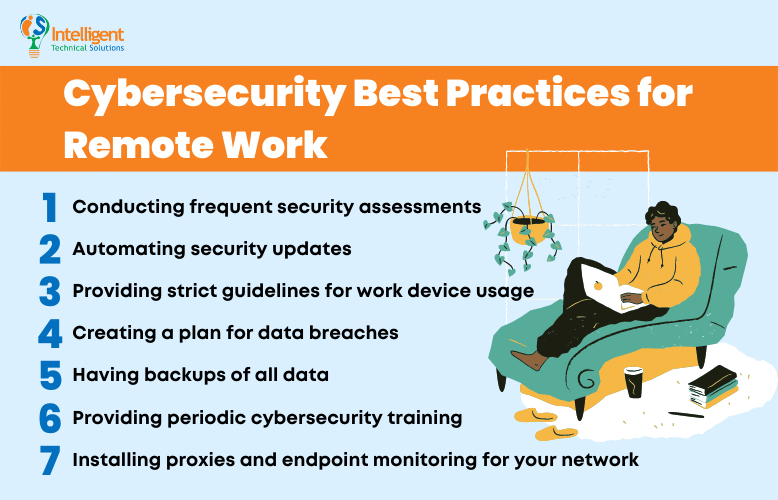
Cybersecurity Best Practices for Remote Work
We invited Edward Griffin, our ITS Partner for Security, to talk about the best cybersecurity practices for remote companies.
By the end of this article, you’ll have the knowledge you need to keep your company safe even while working from home.
1. Conducting frequent security assessments
The first step to protecting your network is identifying your cybersecurity strength across your entire organization. Ask questions like:
- What are the key features of your system?
- What hardware and software do you have?
- Who uses your servers and frequently communicates with one another?
- Who are the high-risk people in your network?
You’ll already be miles ahead of other businesses by having a clear idea of where your cybersecurity is at and constantly checking if you’re maintaining the same level of security.
2. Automating security updates

After conducting your first security assessment, utilize technology to automate updates for you and your staff.
Luckily, offsite technical support has improved by leaps and bounds and is now the first line of support for Managed IT service providers. However, it still requires your IT department to have specialized knowledge about offsite and onsite technical support. With no (or minimal) onsite support, you need to have a streamlined process to reach your employees quickly if anything goes wrong.
You need clear plans to implement essential security updates and help your staff with their technical issues.
“People underestimate everything that goes into making an IT network secure,” Griffin warned. If a hacker can find a way into your system because you didn’t update your printer, that is a huge security gap. Remember, you are only as strong as your weakest link.
3. Providing strict guidelines for work device usage
One of the biggest mistakes is letting remote staff use whatever device they want to access your servers. If a team member is accessing sensitive data with their device, you need a robust onboarding process to install security programs and remove security gaps.
You need more stringent authentication protocols in a remote work set-up. It’s not enough to have strong passwords; there must be multiple layers of security, such as network proxies, 2FA and MFA, and a consistent cybersecurity auditing process.
Some helpful questions to think about when creating guidelines for work devices are:
- What programs can you use to keep your remote workers secure?
- Do you need a new firewall or an onsite server?
- Are you going to roll out a security update or implement a new authentication method?
After answering these questions, you’re ready to step up your organization’s cybersecurity.
4. Creating a plan for data breaches
No company is 100% secure - even tech giants like Cisco and Microsoft experience data breaches. In the current tech environment, it’s better to think of hacking as a certainty, which will give you time to prepare measures to keep your business afloat in case you’re breached.
5. Having backups of all data
How do you ensure you don’t lose data with constantly moving pieces in a remote set-up? Should you back up every device or just the core servers? What schedule should you use to keep everything backed up in your system? How do you do this quickly and efficiently without disrupting any workflow?
These are questions you need to answer when considering remote cybersecurity. Backup and disaster recovery plans need to be expertly planned, with thorough testing to ensure they’ll work in case of a crisis.
Read: How to Make the Disaster Recovery Plan You Wish You Had
6. Providing periodic cybersecurity training.

Your people are your most significant network risks. It’s too easy to let down our guard and accidentally download malware or be fooled into giving out network information.
That’s why it’s crucial to have constant security awareness training to keep your team up to date with current cyber threats and instill the zero-trust mindset.
Your company relies on your IT department and staff to secure your IT infrastructure, so you must ensure you get the best people you can. They must have the proper knowledge and experience to implement all the tips and tricks of cybersecurity.
Some IT experts are:
- CIOs (Cybersecurity Information Officers)
- Managed IT & Co-managed IT providers
- Managed Security Service Providers
- Vetted in-house IT staff
7. Installing proxies and endpoint monitoring for your network
One of the most significant cybersecurity challenges in remote work is endpoint security. If a device can access your network, it’s an endpoint.
It quickly becomes a struggle to ensure each endpoint is adequately protected. With all the desktops, laptops, cellphones, landlines, servers, firewalls, and routers (and more!), you’ll need an application proxy and endpoint monitoring programs for your network.
Need help implementing cybersecurity practices for your business?
You must watch out for constant threats to your endpoint and server security while preparing backup and data recovery plans, device maintenance guidelines, and troubleshooting processes.
And while you can handle these cybersecurity challenges for remote work by implementing best practices like conducting frequent security assessments, automating security updates, and providing strict guidelines for work device usage, among others, that doesn’t mean it’s easy.
Keeping your goals in mind helps you take the first step toward a more secure system. As an MSSP, we know the work can be overwhelming. But Griffin said,
“[Companies] should look at IT from a value and return on investment perspective as opposed to a straight dollar number.”
To take the first step to secure your remote workers, read our article What Businesses Need to Know About Managed Cybersecurity Services.
Kharmela Mindanao is a senior content writer for Intelligent Technical Solutions. She’s called Ella by her friends and likes yoga, literature, and mountain climbing. Her favorite book is Anxious People by Fredrik Backman. She creates art and poetry and is on a quest to find the best cheesecake.
Topics:
