Best Practices for Businesses to Use Public Cloud Safely
June 1st, 2022 | 3 min. read

It doesn't matter what it's attached to; the word "public" will always evoke feelings of danger or discomfort. The reason for that is that we associate it with risk. If something is public, that means strangers can access it, and you have limited control over it, and that's risky. The same goes for your cloud service.
Public cloud services can be cost-efficient and highly accessible. In fact, chances are your team is already using some form of it in your organization. The problem is using them carelessly can pose a higher risk for your data.
Sure, many providers take outstanding measures to secure your information on their servers. However, there's a loophole: they can only ensure data is secure from their side. Unless you're practicing good security hygiene on your end, cloud service providers (CSPs) aren't responsible for what happens outside their scope of influence.
That's why it's essential to practice safe habits when using public cloud services. At ITS, our team are advocates for raising cybersecurity awareness for businesses. In this article, we'll share some of the security risks and best practices when using public cloud solutions.
What is Public Cloud?
A public cloud is a platform that uses the standard cloud computing model to make resources like virtual machines, applications, or storage available to users remotely. Unlike private clouds, wherein you use your own infrastructure, public clouds utilize a shared infrastructure. That means a provider owns and operates computing resources and shares across multiple tenants via the Internet.
Some public cloud services are offered for free or through a variety of subscription or on-demand pricing schemes, including a pay-per-usage model. The most prominent examples of public clouds include Amazon Web Service (AWS), Google Cloud, and Microsoft's Azure.
Security Risks of Public Cloud
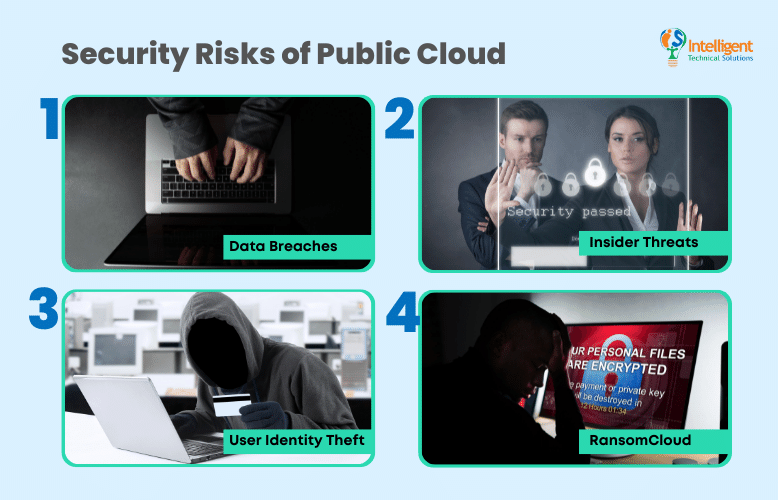
Public cloud services are secure, but only if you use them properly. Otherwise, there are some potentially dangerous threats that you need to be wary of. Take a look below at some of the risks of using public cloud services:
Data Breaches
According to a global intelligence firm IDC study, almost 80% of the companies surveyed had experienced at least one cloud data breach in 2021. This was due to multiple factors such as misconfiguration errors, lack of visibility across settings, inadequate access controls, and even shadow IT.
Insider Threats
One of the top public cloud security issues is unauthorized access to data. Many cloud users fail to set up adequate access controls allowing malicious insiders to take advantage. They can simply walk in and get the data they need.
User Identity Theft
Cloud account hijacking is a common practice in identity theft scams. It's a process where a cyber actor takes over an individual or organization's cloud account. The attacker then uses information from the stolen account to perform malicious or unauthorized activities.
RansomCloud
RansomCloud refers to a certain type of ransomware attack that targets data in the cloud. Just like ransomware, attackers will steal, install malware or encrypt your files to keep you from accessing valuable data and then hold it for ransom.
Best Practices When Using Public Cloud
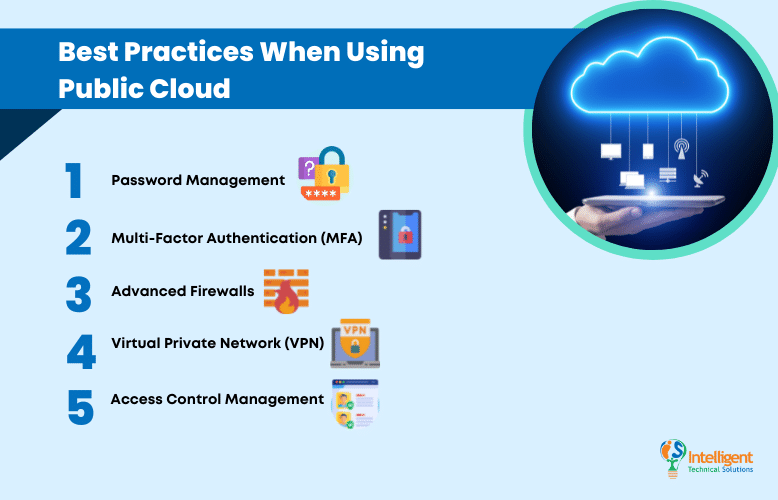
Thankfully, there are simple and easy ways to secure your use of public cloud services. Check out some of the best practices for using a public cloud safely:
Password Management
Creating a strong password and changing it periodically is one of the most effective ways to secure your data in the cloud and also one of the cheapest. Good password management is essential to protecting your company's sensitive information online. Doing so could help your business prevent one of the most common attack vectors on the planet; leveraged credentials. In fact, 61% of breaches are attributed to hackers using the victim's passwords.
Multi-Factor Authentication (MFA)
But what happens if the bad guys still manage to get your cloud account password? That's where MFA can help. It helps add another layer of authentication to help keep intruders out of your network even when they get a hold of your password. It's an easy and affordable method that adds a lot to your cybersecurity posture.
Advanced Firewalls
Having firewalls for your network is one of the very basics of cybersecurity. However, there's nothing basic about the newest iteration of firewalls. Next-gen firewalls (NGFW) have the capabilities of a traditional firewall and combine them with network device filtering functions. These include in-line deep packet inspections, intrusion prevention systems, and more.
Virtual Private Network (VPN)
A VPN is a must when using public clouds. It enables you to extend a private network across a public network, like creating a secure tunnel between one endpoint and the cloud. It allows users to send and receive data across shared or public networks as if their computing devices were directly connected to the private network.
Access Control Management
Don't give access to your cloud to staff who don't need it. The best way to prevent malicious insider threats is stringent access control management. It restricts access to those who don't need it and gives it to those who do. If you're not sure a team member needs access, err on the side of caution and don't authorize them. You can always provide them conditional access later on.
Need Help Using Public Cloud Securely?
Public cloud may pose some risks to your data, but some of the benefits they offer are too good to pass up, especially for businesses that need flexibility. Thankfully, there are a lot of effective and affordable ways to access them securely. All you have to do is practice good cyber hygiene like creating strong passwords, using MFA, firewalls, VPNs, and access control management.
At ITS, we've helped hundreds of businesses manage and secure their cloud migrations. If you want to learn more, read our article on how to choose the right cloud service provider.
Mark Sheldon Villanueva has over a decade of experience creating engaging content for companies based in Asia, Australia and North America. He has produced all manner of creative content for small local businesses and large multinational corporations that span a wide variety of industries. Mark also used to work as a content team leader for an award-winning digital marketing agency based in Singapore.
Topics:
