What is Network Scanning? (& Why is It Important for Your Business?)
February 15th, 2023 | 4 min. read
%20(16)-1.jpg)
Knowing what goes on in your network is critical for ensuring the systems and devices are running optimally. To do that, you need to conduct network scans: the regular auditing of your network for vulnerabilities that might require immediate attention from your IT.
And here at Intelligent Technical Solutions (ITS), we help hundreds of businesses understand their technology and protect their network by providing advanced and suitable security solutions.
We’ve sat down with Rick Catron, one of ITS’ Solution Consultants, to talk about what network scanning is, its types, and why businesses need to get one on a regular basis.
After reading, you should have a clear knowledge of how the process of network scan works and how it can benefit your organization.
What is network scanning?
For easy troubleshooting, you need to understand where your tech problems are coming from. And network scanning helps you with this. It lays out what devices are on your network, their performance, and the traffic moving between them.
It is done using a tool or agent that sends a packet or ping to a network and gets a response to determine the status of the application or devices.
Network scans fall into two categories:
- Passive network scanning which tracks data packets moving through a network trying to find any irregularities, and
- Active network scanning which uses pings or packets to look for specific abnormalities within the network.
These two categories are further divided into different types of network scans.
What are the types of network scans?
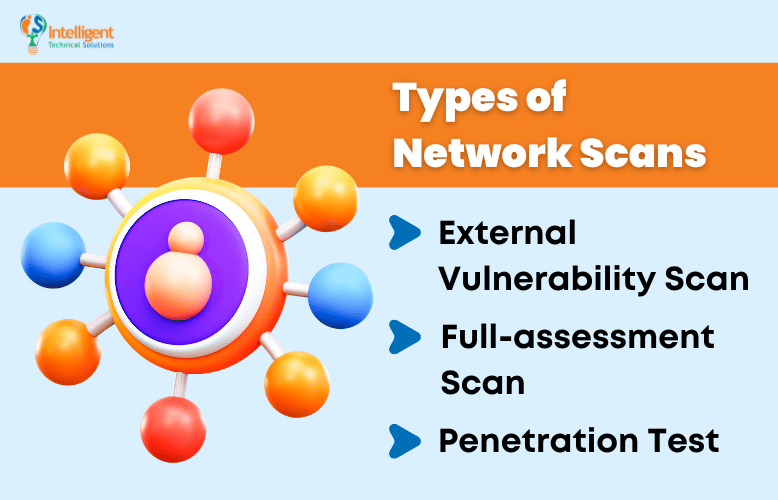
Your organization can deploy three different types of network scans: external vulnerability scans, full assessment scans, and penetration tests.
1. External Vulnerability Scan
“External vulnerability scan primarily lets you know what things are potentially open to hackers,” Catron says.
This type of network scan looks for holes in your network firewalls where malicious outsiders can break in and attack. It answers questions like:
- Do you have the Internet of Things (IoT), and is something open there?
- Do you have an open port on your firewall?
- Are some of your PCs not patched correctly and showing up on the internet?
… and more.
External Vulnerability Scan can answer these questions and basically look at your network from a hacker’s perspective.
2. Full-assessment Scan
The full-assessment scan allows you to get an assessment of all of the network devices from computers, printers, servers, and other devices that are showing up on the network IP address.
It also shows the security status for user accounts from the last time they logged in and how many machines were not patched correctly.
Full-assessment scanning also sees through other vulnerabilities like the lack of antivirus programs or having an outdated one.
3. Penetration Test
“Penetration testing is like external vulnerability scanning but takes it a step further,” Catron explained.
The penetration test finds those holes, and per the client’s or the prospect’s permission, it goes inside the network.
So it’s intentionally penetrating the network; it’s going past the outer layer into the network, seeing what data it can reach, what devices it can possibly take over, and just what is potentially at risk for a client or prospect.
Read: Uncover Your Business's Vulnerabilities with Penetration Testing
Why do businesses need to get their networks scanned?
With hundreds of devices continuously connecting and disconnecting from your network, ensuring the network’s availability and operability has become more challenging. That’s why companies are urged to do regular network scans for reasons beyond security.
So, why should businesses like yours need your network scanned?
1. It gives you peace of mind.
 Suppose you’re working with an IT support provider, and whenever you ask them for updates, they always tell you that “everything is great,” “you have nothing to worry about,” or anything along those lines.
Suppose you’re working with an IT support provider, and whenever you ask them for updates, they always tell you that “everything is great,” “you have nothing to worry about,” or anything along those lines.
You’ve been working with them for quite a while, and they’ve been very helpful, so you trust them fully. However, there will be days when you just want to cross-check their reports to the actual results to make sure nothing is wrong–or will go wrong.
Regular network scanning is the way to do that.
It lets you verify that you have the proper security in place for continued productivity and protection.
“There’s a saying that I always use with people; it’s called trust but verify. Trust the people you work with but verify the results.” Catron shares.
2. It helps provide an accurate proposal before onboarding.
 If you’re just starting with a new Managed IT Service Provider (MSP), a network scan will be beneficial for both parties by removing unexpected obstacles after onboarding.
If you’re just starting with a new Managed IT Service Provider (MSP), a network scan will be beneficial for both parties by removing unexpected obstacles after onboarding.
It helps your provider create a suitable security solution that can cater to the number of users you have on your network. It even helps with pricing, as the right quotation depends on the initial assessment.
Your MSP will discover the exact number of computers, servers, and data they need to protect to be able to do their job and offer you an accurate proposal.
Many things could go wrong if you don't do a network scan prior to onboarding. For example, you could already come on board, and your MSP finds out that you’ve got double the number of computers, servers, or data than what you stated. Then, it would be a big problem for your data security and your budget.
3. It highlights potential security issues during onboarding.
 Having a network scan could highlight potential security issues that need to be addressed more readily during the onboarding, issues that you yourself may not be aware of.
Having a network scan could highlight potential security issues that need to be addressed more readily during the onboarding, issues that you yourself may not be aware of.
“They could say they’ve got twenty computers, but what if they have seven machines that they didn’t know were still Windows 7?” Catron said. “With a network scan, we could ask the client to automatically start preparing for the replacement before they even fully onboard with us. It also prepares the clients for the fund needed to address unknown issues, like that outdated machine.”
Need help with network scanning?
A network scan allows your organization to detect weaknesses and existing issues, so you can handle them and focus your efforts on growing your business. As a recap, here are the most common types of network scanning processes you can deploy:
- External Vulnerability Scan
- Full-assessment Scan
- Penetration Test
At Intelligent Technical Solution, we require clients to undergo a network assessment, which includes a network scan, to help them analyze their requirements and identify growth opportunities.
We've been doing this for the past decades as a Managed IT Service provider before we onboard clients. Watch this video to know what our onboarding process is or schedule a meeting with us today to know how we can help you.
Jess is a Content Writer who commits herself to creating helpful, relevant, and easy-to-digest technical articles. When she isn't writing, she devotes her energy (and money) to collecting K-Pop photo cards, which she likes to call an 'investment.'
Topics:
