How to Reinforce Your Cybersecurity During Pandemic?
May 23rd, 2022 | 3 min. read
Many small businesses were severely affected by the pandemic simply because most were forced to stop their operations and a huge margin transitioned to a remote work setup unprepared.
While many of us are spending time trying to make sense of this new normal, hackers are in high gear exploiting the network vulnerabilities of your business. As usual, they are on the lookout for important data that they can sell for a quick buck or hold for a hefty ransom.
According to a recent study, cyberattacks have increased by nearly 500 percent since the pandemic started. Worse, damages caused by digital attacks grew by $1.07 million in last year alone— the most significant increase for the past 17 years.
As we continue living through this pandemic, you can expect that cybercriminals will continue to operate their schemes. If you don’t want your business to be part of the statistics, then you must stay on high alert and put up a strong defense against cyber threats.
Here at Intelligent Technical Solutions (ITS), we help hundreds of businesses secure their network using comprehensive cybersecurity solutions and continuous education about cyber threats.
In this article, we’ll share practical ways to boost your cyber security to keep your business and your clients safe from cyber attacks.
3 Ways to Strengthen Your Cybersecurity
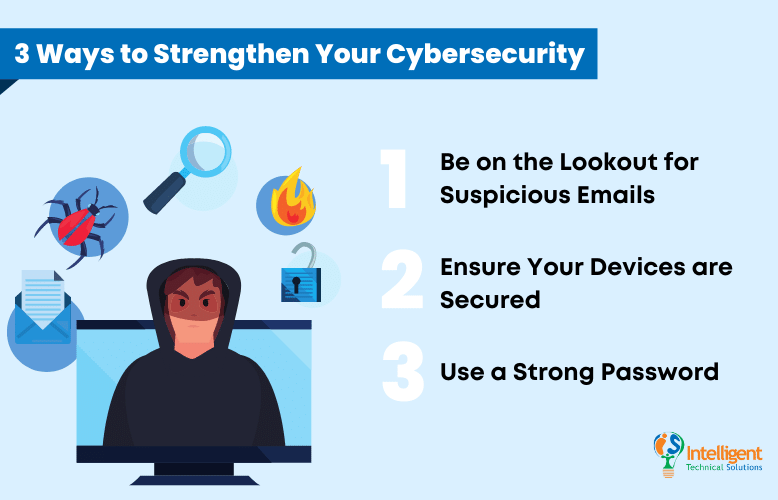
1. Be on the Lookout for Suspicious Emails
Email is one of the favorite attack vectors of cybercriminals. They may disguise themselves as representatives of legitimate businesses reaching out to you about your compromised account. But their actual goal is to get your guard down so that they can steal confidential information and financial data from your company.
This type of attack is called phishing. Attackers try to reel in their prey by sending them a compelling message. Their emails usually contain links to bogus websites. If visited, they can steal your credentials or install malware on your device that can take valuable information.
Here are some telltale signs of a phishing email
![]()
- Threats or a sense of urgency
- Grammar and spelling errors
- Inconsistencies with the email address and website links
This type of attack can easily be avoided. Don’t reply and never open the links nor download any attachments. Delete their message immediately and notify your IT Team about it. Remember, damage can only occur if you take the bait.
2. Ensure Your Devices are Secured
Another cause of the surge in cyber-attacks is the dramatic increase in employees working-at-home. As many businesses transitioned their workforce to remote setup, the risk of data exposure also increased. This is because the typical home network doesn’t have security as robust as your office setup.
However, this doesn’t mean you can’t protect your network from cybercriminals when working remotely. There are still several steps you can take to prevent hackers from breaching your business. Here are a few:
- Use updated antivirus and internet security software
- Utilize VPN (Virtual Private Network)
- Set up a Multi-Factor Authentication
3. Use a Strong Password
Hackers now use different tactics in cracking passwords, such as brute force, dictionary attacks, keyloggers, and others. This means using your pet’s name as a password is not a good idea, even if you match it with your birthdate.
For this reason, we urge everyone to create a unique password that’s hard to decipher, even for software. Here are some tips that you may find helpful in creating and updating your password:
- Don’t use names of your relatives, partner, or even pets
- Use a combination of capital and small letters, numbers, and special characters
- Use at least 12 characters
- Do not use identical passwords on different accounts
We understand that some businesses use many tools, with each requiring a separate account. This may lead to confusion and, worse, lockout. To avoid mixing up passwords and prevent being blocked from your system, we suggest using a password manager app like LastPass.
Password managers are a great way to save and organize your passwords without the risk of exposing it to cybercriminals. It uses several layers of authentication to ensure that only you have access to your info.
Remember, using weak passwords makes you and your business vulnerable to cybercriminals.
Is Your Business Secured Against Cyberattacks?
As cyberattacks continue to rise this new normal, it’s vital for our network defenses to adapt. Simple steps such as using a strong password, constantly updating your antivirus software, and scanning your email for suspicious messages can go a long way in preventing cyber criminals from breaching your system.
It’s also essential to make sure everyone in your team is practicing their best in ensuring your network's safety. As the saying goes, “A chain is only as strong as its weakest link.”
Here at ITS, we’ve helped businesses create strong defenses against cyber threats by providing the best cybersecurity programs. If you wish to learn more about how you can protect your business from cyberattacks, we suggest watching our video entitled 15 Ways to Protect Your Business from a Cyber Attack.
Topics: